Even (especially) if you’re in a small law firm, chances are high that your passwords are exposed on the dark web and waiting for the highest bidder. But as Tom Lambotte explains, you don’t have to wait for the creepy emails and ransom demands to find out.
Let’s imagine you found out that burglars had copies of your house key. Would you want to know? And how long would you wait to address the threat? I’m guessing you’d have a locksmith on the phone ASAP to come and change your locks.
Fortunately, no burglars have copies of your home key.
However, chances are incredibly high that your digital credentials (emails and passwords) — aka the key to your digital life — are currently for sale and in the hands of criminals.
Can you imagine the havoc a data breach would create for your solo practice or small law firm?
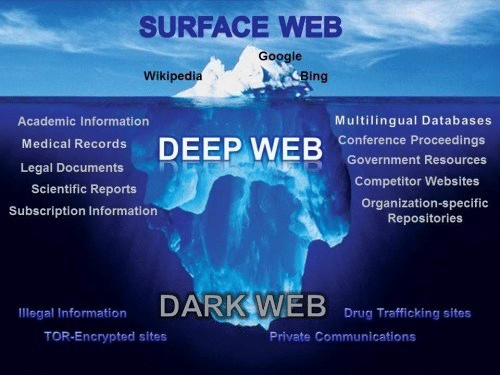
What Is the Dark Web?
There is often confusion about the dark web. It is a difficult concept to grasp. Let me try to simplify it.
The dark web is a hidden universe within the “deep web” — a sublayer of the internet hidden from conventional search engines.
Search engines like Google, Bing and Yahoo only search 0.04% of the indexed or “surface” internet. This is the part of the web you are most familiar with.
The other 99.96% of the web consists of databases, private, academic and government networks, and the dark web. The deep web is estimated to be 550 times larger than the surface web and growing. Because you can operate anonymously, the dark web holds a wealth of stolen data and illegal activity.
The dark web is the hidden marketplace for criminals.
Digital credentials such as usernames and passwords connect you and your firm’s staff to critical business applications and online services. We’re talking credentials for Office 365, Dropbox, Box, Clio, Adobe DC, and even your bank accounts. Unfortunately, criminals know this — and that’s why digital credentials are among the most valuable assets found on the dark web.
The dark web is made up of digital communities that sit on top of the internet. While there are legitimate purposes to the dark web, it is estimated that over 50% of all sites on the dark web are used for criminal activities, including the disclosure and sale of digital credentials. Think Amazon for cybercriminals.
Far too often, companies that have had their credentials compromised and sold on the dark web don’t know it until law enforcement has informed them.
OK, if you’re in a small firm, you may be mentally checking out.
You may be telling yourself, “That sounds like a threat for BigLaw to be concerned with, my law firm’s too small. We’ve only got 12 people here — criminals won’t take their time to come after us.”
Or, “I’m a solo, cybercriminals don’t have a target on my back. I’m not worth their time.”
Flawed thinking.
Solo and Small Law Firms Are Preferred Targets
Hackers know that the smaller businesses are, the fewer protections they have in place. Yet they typically have access to valuable confidential information such as patents, financials, contracts and especially personal information (date of birth, SSN, etc.).
Compromised credentials are used to conduct further criminal activity, such as breaches of sensitive information and identity theft of individual employees. Users often have the same password for multiple services, such as network logon, social media sites, online stores and other services, exponentially increasing the potential damage from a single compromised username and password.
Think about this.
You might not worry about the LinkedIn hack (117 million) or the Yahoo hack where criminals stole a record-shattering 3 billion (that ‘b’ is not a typo) credentials.
Who cares if they got into your LinkedIn account? Or if they got the username and password from your Yahoo account, which you haven’t used in seven years?
Research shows that employees often recycle passwords throughout their work and personal networks. Suppose your internal requirement is to include a capital letter and a unique character. In such cases, it’s common for employees to use a password they are familiar with and add a capital letter and exclamation mark. (Here’s an example. Exposed Password: cowboys; Variations: Cowboys!, Cowboys1, Cowboys!1, and so on.) Knowing this, hackers will run scripts using Metasploit frameworks (hacking and pen testing tools) to “brute force” their way into unsuspecting systems.
These scenarios are real — but the odds are low that anyone in the firm knows of it until after a breach.
For example, one client learned that a paralegal had used his work email address to create an account on a dating site while another three users did the same with a Facebook account, each of which had been hacked. The firm had 29 other instances of its hacked digital credentials being sold online.
This firm drastically lowered its risk of a breach by proactively monitoring the dark web for credentials and taking action on any results coming up.
What Can You Do About the Dark Web?
It bears repeating that creating strong passwords, ideally using a password manager, is a good first step to keep digital credentials safe. If you save any passwords in your browser, you can also use the browser’s free tools (Google Password Check and Mozilla Firefox Manager, for example) to check if your passwords have been compromised. Password “check” tools, however, only help you after the fact.
Be proactive.
Dark web scanning tools can provide around-the-clock alerting and monitoring for signs of compromised credentials. These tools scour sources such as botnets, criminal chat rooms, peer-to-peer networks, malicious websites and blogs, bulletin boards, illegal black market sites, and other private and public forums. You are alerted when credentials go online. So, armed with this information, you can take action to change all instances and variations of compromised passwords for any user in your firm, reducing your risk of a data breach.
Dark web scanning and monitoring are among the multiple strategies you should be leveraging to protect your firm from cyberattacks. To fully protect your firm, you must employ a multilayer solution; cybersecurity is an ongoing process that requires vigilance.
Illustration ©iStockPhoto.com
Subscribe to Attorney at Work
Get really good ideas every day for your law practice: Subscribe to the Daily Dispatch (it’s free). Follow us on Twitter @attnyatwork.